Checkmarx has uncovered a new and sophisticated cyber threat targeting the banking sector.
The security testing firm’s research team detected two distinct open-source software supply chain attacks targeting financial institutions. These attacks, which involved advanced techniques and deceptive tactics, have raised alarm bells among cybersecurity experts.
Attack one: NPM
The first attack occurred on April 5th and 7th when a threat actor exploited the NPM platform, uploading packages with a preinstall script designed to execute malicious activities upon installation.
Notably, the contributor behind these packages was linked to a fake LinkedIn profile posing as an employee of the targeted bank. The bank, unaware of the activity, quickly became a victim.
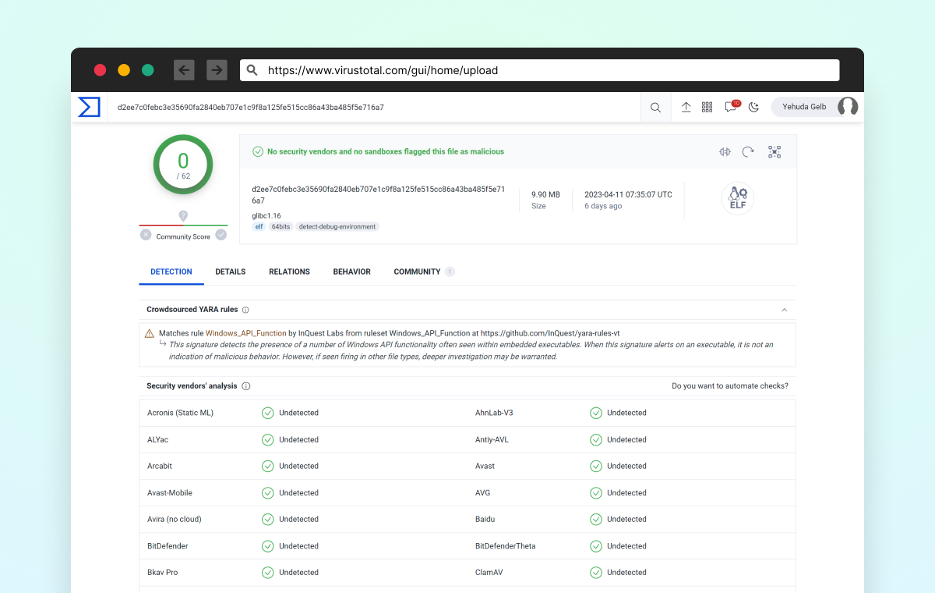
The multi-stage attack involved identifying the victim’s operating system and decoding encrypted files within the NPM package to download a second-stage malicious binary onto the victim’s system. The Linux-specific encrypted file escaped detection by widely-used antivirus services, allowing the attacker to maintain a covert presence on Linux systems.
Furthermore, the attacker cleverly used Azure’s CDN subdomains to deliver the second-stage payload—exploiting legitimate domains to bypass traditional defense mechanisms.
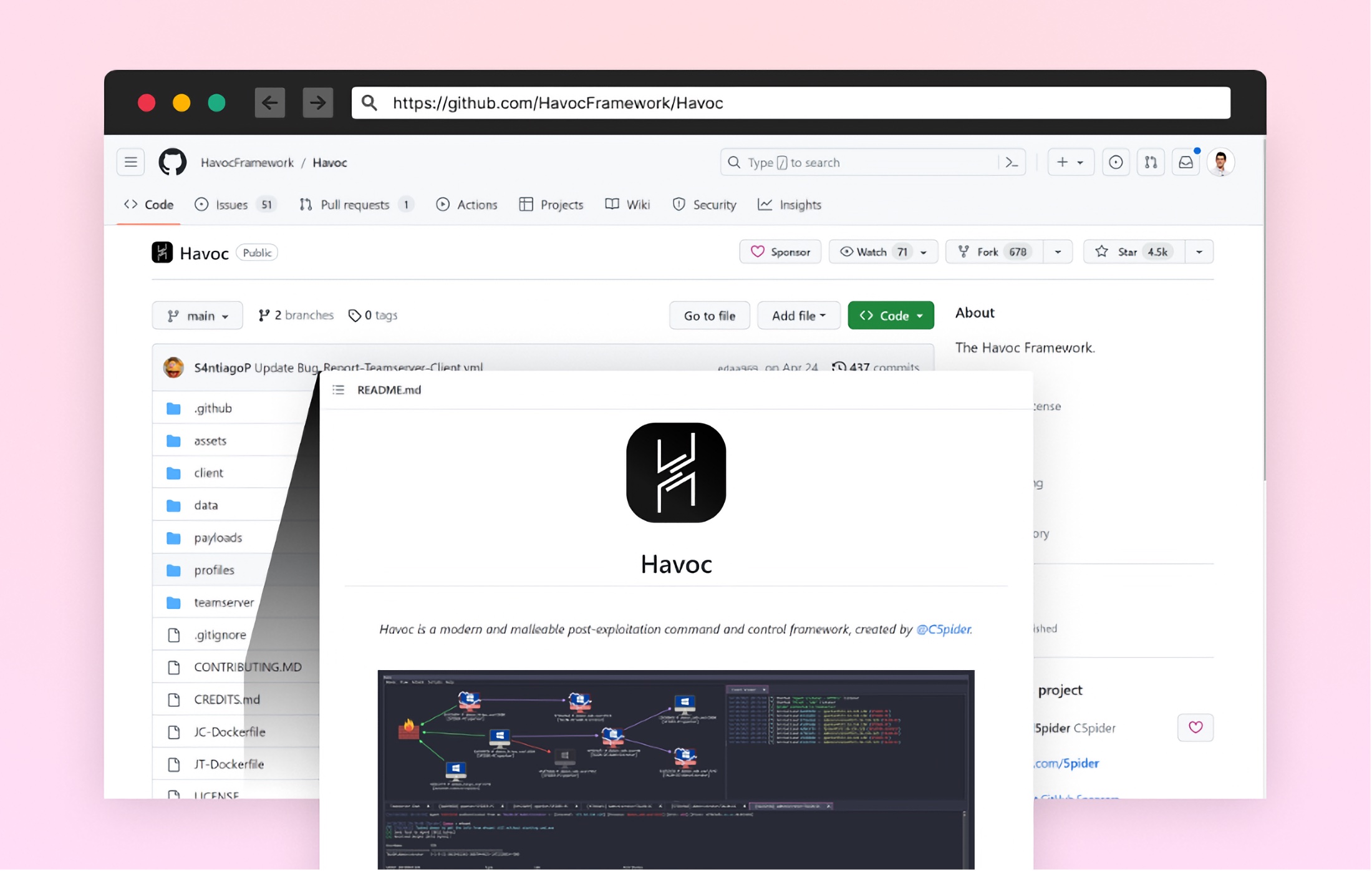
The Havoc Framework, a powerful post-exploitation command and control tool, played a key role in evading detection.
Attack two: Masterful payload integration
In February 2023, a different group of cybercriminals targeted another bank with a distinct approach.
This attack involved uploading a package to NPM containing a carefully crafted payload that blended into the victim bank’s website. The malicious code lay dormant, intercepting login data and transmitting it to a remote location when activated.
Evolving supply chain security
These attacks have underscored the inadequacy of traditional vulnerability scanning at the build level. Once a malicious open-source package enters the software development pipeline, it becomes an instant breach, rendering subsequent countermeasures ineffective.
To bolster defenses against these evolving threats, industry-wide collaboration and proactive security measures throughout the Software Development Lifecycle (SDLC) are essential.
Organisations must differentiate between regular vulnerabilities and malicious packages and adopt integrated security architectures to prevent infiltrations proactively.
Further attacks
Experts predict a continued trend of attacks against the banking sector’s software supply chain.
As cyber threats become increasingly sophisticated, continuous vigilance, adaptation, and knowledge-sharing remain crucial to safeguarding the cybersecurity ecosystem. The banking industry, in particular, must recognise the urgent need to bolster its defenses against these relentless adversaries.
Collaborative efforts and proactive security measures are the keys to maintaining a safe and secure software supply chain environment. By staying ahead of emerging threats and learning from past attacks, the industry can create a stronger and more resilient cybersecurity landscape.
(Image Credit: Checkmarx)
See also: Sonatype uncovers further malicious PyPI and npm packages

Want to learn more about cybersecurity and the cloud from industry leaders? Check out Cyber Security & Cloud Expo taking place in Amsterdam, California, and London. The event is co-located with Digital Transformation Week.
Explore other upcoming enterprise technology events and webinars powered by TechForge here.







